Zero Trust Cloud Security
May 31 2023
What is Cloud Security?
In today's digital world, where businesses rely heavily on cloud services and remote access, ensuring security is of paramount importance. Where businesses and individuals rely heavily on the cloud. As corporations and individuals loved the cloud for its flexibility and scalability, the need for a comprehensive security framework becomes imperative. Zero Trust Architecture (ZTA) comes in role, a revolutionary approach that provides enhanced protection for cloud-based environments.
Understanding Cloud Security
Cloud computing changed the way businesses operate, it also introduces new security challenges. Traditional security models, such as perimeter-based defenses, are no longer sufficient in protecting cloud-based resources. Cloud makes everything applications, and every application has ip, but the traditional model is that every host has ip.
With cloud computing, we create applications and store data in the cloud, We need to protect these applications and data from unauthorized access, breaches, and other cyber threats.
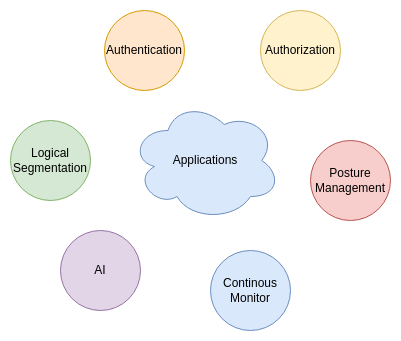
Key Components
- Data Protection
Zero trust ensures that data remains secure, regardless of its location or the device accessing it. Access controls and policies add an additional layer of protection.
- Access Controls
Zero trust's primary goal is managing authentication and authorization, and this approach mitigates the risk of unauthorized access. User and device verification is performed at every interaction.
- Incident Response
With continuous monitoring, Zero Trust enables organizations to detect and respond to security incidents quickly.
- Vulnerability Management
Continuous Vulnerability assessments and scanning are performed to identify and remediate security Vulnerabilities in infrastructure, applications, and dependency libraries.
- Compliance and Governance
Cloud security should align with regulations and compliance requirements.
Conclusion
Zero Trust Cloud Security is a proactive and comprehensive approach. By adopting the principles of identity verification (authenticaton),least privilege, micro-segmentation,continous monitoring, organizations can establish a robust security in cloud environment.